A dependable File Transfer Protocol (FTP) is an essential asset for securely managing and transmitting data. SFTP (Secure FTP) allows users to upload and download documents over the web while ensuring they stay safe from malicious or unauthorized access. You can use it to create secure backups, share files, host websites, and maintain your website.
In this article, we define what is SFTP and what is SFTP used for, provide insight into what’s possible with it and highlight its security protocols.
What Is SFTP?
Secure File Transfer Protocol (SFTP) is an FTP application that allows users to transfer files via a protected channel using the SSH protocol. It offers added surveillance features such as authentication to ensure that only recognized users can access the data. SFTP also enables strong encryption of data and file transfers, which keeps data private from malicious third parties.
Unlike FTP Secure (FTPS), which uses multiple port numbers for file transfers, Secure FTP uses a single port. Using multiple ports under FTPS requires opening a range of ports in the firewall, which is a security risk. In contrast, SFTP does not have that risk.
SFTP also encrypts data transfers with the SSH protocol, offering an extra layer of security for files that are being shared, backed up, hosted, or maintained. SSH protocol (Secure Shell) also provides data integrity and surveillance and prevents hackers from stealing or altering data during transfer.
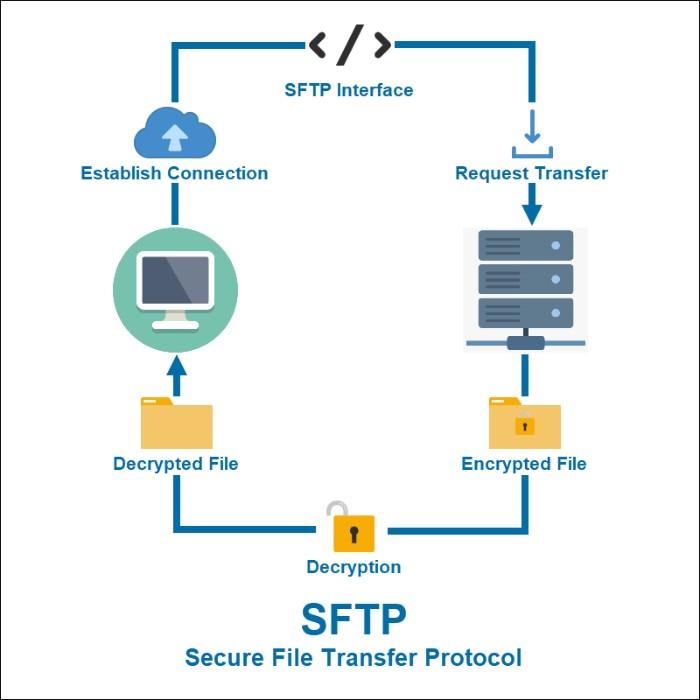
How Does SFTP Work?
SFTP connects the client and server applications via an SSH tunnel. The server application requires authentication from the client to ensure the user is authorized and then uses SSH encryption to protect data during transmission.
Once authenticated, data is transferred between the two applications through this SSH tunnel. The client can initiate a file or directory transfer using specific commands like “get” or “put” sent over an encrypted connection. The recipient then receives the file or directory and processes the transfer according to its instructions.
You can use it to:
- Back up files securely over the web through encryption
- Share files with others using encrypted channels
- Host websites and other services securely on servers
- Maintain websites and databases securely by performing server maintenance tasks
- Automate file transfers with scripts and commands by the client or server applications
SFTP uses a client-server model, with a Secure FTP client connecting to the server. The same tools used for FTP can be used for SFTP, but specialized software known as SSH File Transfer Clients is developed specifically for SFTP connections. They come with extra features, such as user authentication and encryption, that make them suitable for secure file transmission.
SFTP also provides an extra layer of security by using SSH keys for authentication. An SSH key is a set of two cryptographic keys: private and public keys. The private key remains in your computer, and the public key is shared with the server. Upon authentication, the server uses the public key to verify the user’s identity and allows access to the file transfer. This is a much more secure method of authentication than passwords since external parties can’t guess or hack the private key itself.

What Is SFTP Used For?
SFTP is the perfect tool to:
- Protect your customers’ personal information: SFTP is the ideal file transfer solution that guarantees compliance with industry standards.
- Combat hackers and other unauthorized users: a secure method for keeping confidential information safe as it is transported.
- Enhance the security of your online transmissions with a VPN: You can use SFTPs with VPNs to provide unrivaled data protection through their encrypted tunnels.
Benefits of Using SFTP
Advantages of using SFTP include:
- Data security and privacy: No unauthorized user will have access to your files since they’re encrypted during transmission with SSH.
- Strong authentication methods: SSH keys ensure user identification is secure, reliable, and tamper-proof.
- Robust automation capabilities: Commands used for file transfer can be automated and programmed into scripts for file transfer.
- Cost-effective: This protocol is open-source software that does not require license fees, which makes it cost-effective and reliable.
Disadvantages of Using SFTP
Despite its advantages, SFTP does present drawbacks, including:
- Compatibility issues: Different clients may not support the same commands or protocols as your server application, which can lead to incompatibilities and difficulty transferring files.
- Security vulnerabilities: If you fail to keep your system up-to-date with the latest patches and software updates, you may put your server at risk of malicious attacks.
- Complex setup: This protocol requires technical knowledge to set up a secure connection, which can be difficult for novice users.
How to Use SFTP?
Using SFTP is straightforward and requires a few simple steps:
- Install a Secure FTP client on the computer you will use to transfer files.
- Connect to the server by entering your authentication credentials, such as username and password or SSH key pair.
- Select the file(s) you want to transfer and select the “Send” or “Receive” command.
- Confirm the transfer and wait for the process to be completed successfully.
An example of what this looks like is below:
- sftp [username]@[remote hostname or IP address]
- Enter password:
- Connected to remote-host.
- sftp> ls -l
- drwx—— 7 username group 4096 Sep 21 18:12 Documents
- -rw-r–r– 1 username group 42 Mar 28 11:22 example.txt
- sftp> get example.txt
- Fetching /home/username/example.txt to example.txt
- /home/username/example.txt 100% 42 0.0KB/s 00:00
- sftp> exit
- Connection closed.
When using a Secure FTP client, you can access different options such as file compression, permission settings, checksums, logging, and encryption algorithms. These options can be used to secure your connection and ensure the data transferred is not tampered with or corrupted.
SFTP Examples
To make the most of Secure FTP, common commands you should be familiar with include:
- sftp> put — Upload a file
- sftp> get — Download a file
- sftp> cd — Change the active directory path
- sftp> pwd — Display the remote working directory
- sftp> Icd — Change the local system’s directory path
- sftp> lpwd — Display the local working directory
- sftp> ls — Display contents of the remote working directory
- sftp> lls — Display content of the local working directory
- sftp> lmkdir — Create a local directory
- sftp> lumask — Change the umask value
- sftp> rename — Rename a file on the remote host
- sftp> rm — Delete a file on the remote host
Final Thoughts
Secure FTP is a secure method of transferring files over the internet or between servers. With support for encryption algorithms and permission settings, SFTP helps protect your data from unauthorized access. It also allows you to compress files before the transfer, reducing their size and speeding up the process.
For maximum security when sharing sensitive documents online, SecureDocSharing can help. Keep your files safe with its encrypted document transfer system.
Secure your files with SecureDocSharing today!
FAQs
-
To use SFTP, you need an FTP client software, such as SecureDocSharing. This allows you to connect to the remote server, upload and download files and set permissions and other options. Depending on your setup, you may also need a Secure FTP server and SSH key pair. A basic understanding of file transfer protocols and concepts is also helpful.
-
SFTP typically uses port 22 for communication. You may have to configure your server settings to enable SFTP connections. You can consult the documentation for your specific server or contact technical support for assistance. Make sure your Secure FTP client is configured correctly to ensure secure file transfers.
-
To transfer files using SFTP, connect to the remote server using an FTP client. Once connected, you can upload, download and manage files on both sides. It’s also possible to configure various settings, such as encryption algorithms, for enhanced security.
-
Yes, you need a server to use SFTP. The FTP client will connect to the remote server and transfer files. There is also a need for authentication credentials, such as a username and password, for a successful connection.


